Data Protection Principals. For Leaders in Education, Data Security Matters.

If you’re a College Principal or senior leader in education it’s likely you’ve heard of the #GDPR (if you haven’t you must have been on an almighty sabbatical) and it’s also likely you may think your Director of IT has long sorted it.
If so, you could be facing a rather unexpected problem since your technical team were not, and are not, where the primary risks to data protection reside.
Technical teams will likely get cybersecurity (at least enough to provide a baseline of appropriate assurance) and will have firewalls and wider technical defences already in place (you’d hope).
Your focus shouldn’t be on the technical staff when it comes to data security so if its senior IT staff reporting to the Audit Committee on this, you’ve got it wrong. It’s everyone else in your organisation, aside from the IT staff, who pose the biggest threat to your data protection responsibilities and the solution to it largely isn’t a technical one.
Awkward truth, but a fact nonetheless. No easy quick fix sadly. All the firewalls and software in the world won’t help you when it comes to data protection.
The bottom line is if you haven’t trained every single member of staff from the Cleaner to a Vice Principal on how to stay safe in a digital world then the following information will be of value to you. It will certainly interest your Audit Committee should the worst happen.

According to an analysis of data provided by the UK Information Commissioner’s Office (the ICO) undertaken by CybSafe in 2019 it was actually human error, not malicious criminals, who resulted in more than 90% of data breaches. Let that sink in.
Nine out of ten of all cyber security breaches are caused by human error.
The big message from this analysis for me is that the scale of this human error is increasing, from 87% the previous year and 61% the year before. This trend is surprising given the amplification online safety has had in recent times with the arrival of the GDPR. Additionally research published by Computer Business Review cites just 7% of data breaches as attributable to hostile criminals such as hackers.
Clearly something is going wrong and a likely area of special interest is how educators are being coached and trained, or not, in the ever evolving world of cybersecurity and its associated threats. A paper published by Osterman Research suggested that less than half of organisations had trained their staff at all on data protection good practice despite the potential high impact, likelihood and cost of a data breach.
This is something I see all of the time. Typically, not always but often, colleges and universities will hold a CPD event on data protection once then that’s it. Sometimes it may be repeated a year later, often not. As evidence suggests that new emergent data security threats occur on a daily basis, the flaw with waiting a year to update your training is obvious.
This challenge is not something that a few days of CPD will fix, and the cost of getting it wrong can be catastrophic, as Jeffrey Wong found out.
That’s so Wong
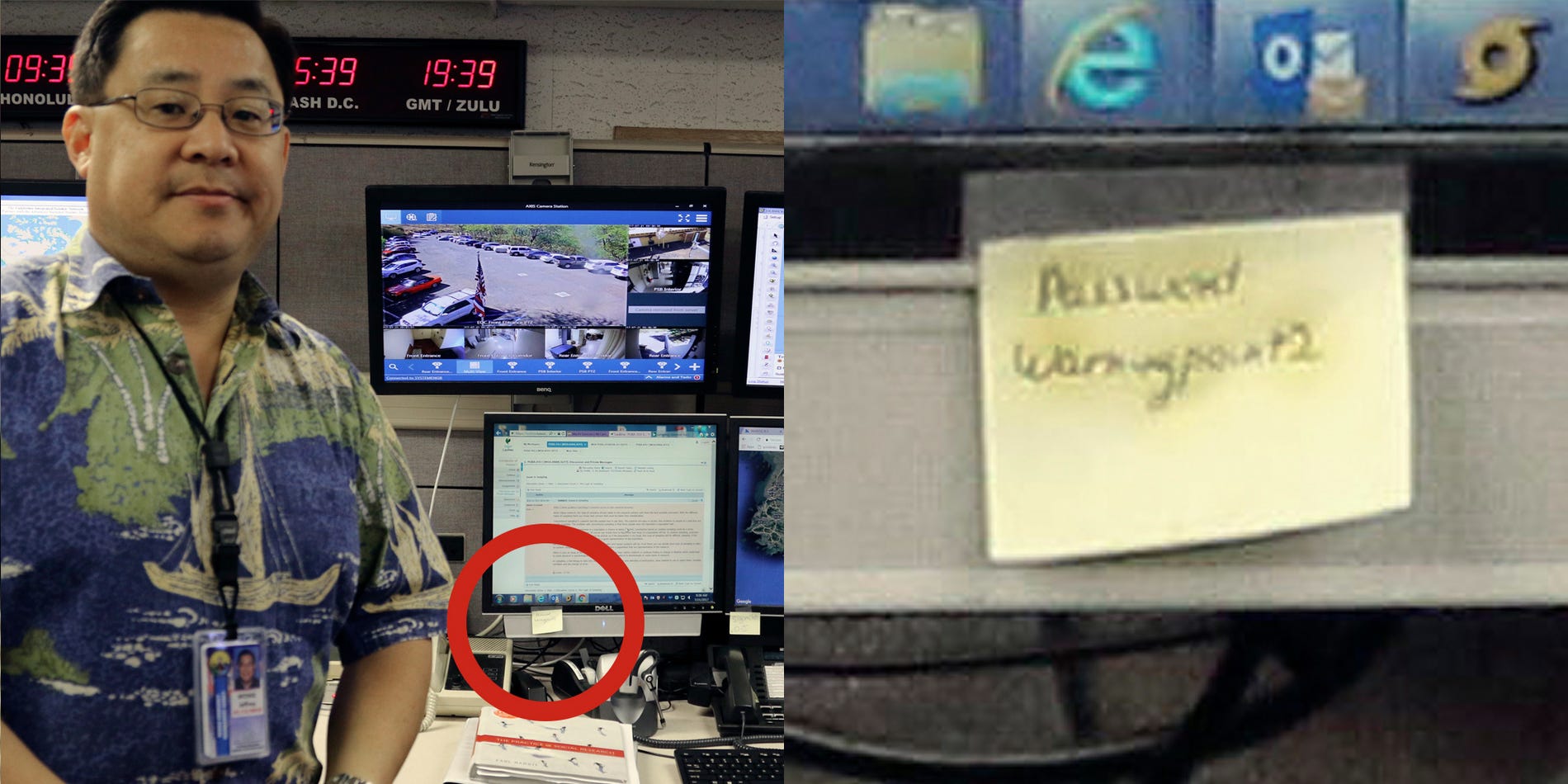
Jeffrey Wong, the Hawaii Emergency Management Agency’s Operations Officer, accidentally went viral. This wasn’t entirely as a result of the false missile warning being issued by the agency causing widespread panic, bad as that was. No we have heard of Jeffrey Wong for a different reason.
During his unplanned media appearance to explain the false missile warning it was noted that behind him, on a sticky note attached to a computer, was a password.
Given the role of the agency in military defence, this was not good. Really not good.
When it comes to cybersecurity own goals, this takes some beating. It should be noted that there’s no evidence actually suggesting that Wong was personally responsible (although you can bet it felt that way) but the damage was done and it certainly raised serious questions about security at the agency.
It’s an easy human error to make but the consequences can be serious.
Let’s explore some wider common own goals to avoid when it comes to data security.
Gone Phishing

According to numerous analyses the most likely human error when it comes to cybersecurity breaches are phishing attacks, loosely translated as either a person or software pretending to be someone else in order to secure sensitive information and usually arriving via email.
I’ve been aware of many close calls when it comes to phishing attacks targeting senior executives (also referred to as whaling as the bosses are the ‘big fish’).
As mentioned one of the possible causes behind the increasing success of such attacks is that cybersecurity training might not have been assessed as an ongoing priority and given appropriate status on the corporate risk register (another thing I see often).
It’s not unusual to find organisations where staff are trained in data protection as part of their induction on joining, then that’s it.
This approach makes an organisation highly vulnerable to cybersecurity issues as threats such as phishing have evolved dramatically in their sophistication as a result of social engineering techniques.
If you were to run a phishing simulation threat assessment in your organisation you may be surprised by how many people fall for it if the test is run authentically (dare you try it?).
Using a leading cloud based email solution that deploys world leading AI and machine learning in the background to continually scan for evolving threats is also a smart idea as part of risk mitigation.
If you’re relying on technology that runs overnight patches to update anti-virus software, you have unnecessary risks and it’s only a matter of time before the weakness is exploited.
Safety device
Another high priority security threat when it comes to data is the use of corporate devices (such as laptops) where staff may share the use of the device with friends and family when outside of the working environment.
Traditional laptops are especially vulnerable to data breaches of this type and represent a higher risk profile when it comes to viruses than comparable devices such as chromebooks which have no need for anti-virus software since they have built in protection against viruses and malware that is continually updated to defend against emerging threats.
As for portable storage devices like memory sticks, that’s just a no. Ban them and do it now.
As a security specialist was overheard saying at a recent conference, ‘memory sticks are the devil’. When it comes to data security they are indeed.
A colleague or student bringing an infected memory stick into college or university has the potential to bypass anything that your IT specialists can do. Ban them. Did I mention you need to ban them? I think I did.
Password123
The bad news is that the whole concept of passwords is a bad idea when it comes to cybersecurity but we are stuck with them for a while. As such, having a complex password is a necessary evil. That said, based on data from the UK National Cyber Security Centre (NCSC) many of us are still not using intelligent passwords with such gems as ‘Blink182’ and ‘Superman’ used regularly.
The most frequently used password where a data breach occurred was ‘123456’ as used by some 23.2 million people who soon regretted it. Seriously. You may be shaking your head at that but before you feel too smug, read on. ‘Password’ was also included as the, well password, on some 3 million accounts.
If you were thinking of including the names Ashley or Michael with some number combination, don’t. Really don’t do that. Same goes for Jessica or Charlie.
Football fans also seem very keen to use their team names in their passwords and feature highly on the NCSC list of shame with Liverpool topping the list, followed by Chelsea and Manchester United with ‘manutd’ being a commonly compromised element to passwords. I am assuming that Stoke City doesn’t feature because their fans use superior passwords.
Swear words also featured commonly with ******* and ********** topping the list, so don’t use those.
Bottom line, use a complex password and two factor authentication. Not ideal, but necessary, and don’t write your passwords down on paper marked ‘passwords’ and stick it to the computer you use on a sticky note.
That’s a bad idea also, especially if you’re running something sensitive like a missile defence centre.
Prioritise high priority accounts
Having stated that the IT team is not your biggest risk, there is a key responsibility they have to get right around the management of security protocols for high privilege accounts, those admin level accounts that hold the keys to your castle.
Effective security protocols around passwords for high privilege accounts preventing their misuse is essential, especially if your technical teams have kids called Ashley or Jessica. If these accounts are compromised the consequences can be severe so regular security checks and audits are a must.
As a minimum your technical team should follow a least privilege principle when it comes to account management with elevated privileges on a ‘as needed’ basis, not a blanket right.
Return to sender
Ever sent an email to the wrong person or one you wish hadn’t been sent at all?
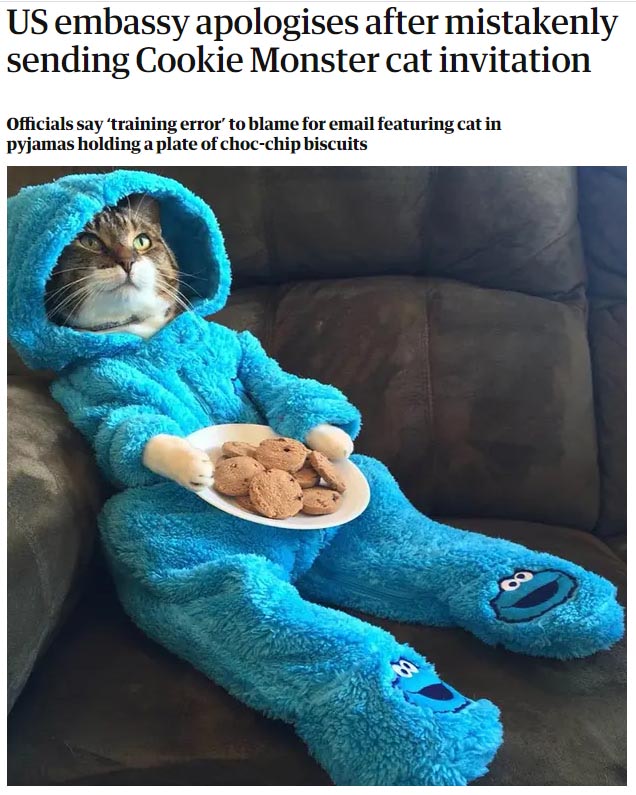
Many people have. In fact it’s one of the most common causes of a data breach (the 4th most common according to research by Verizon) accounting for more than 60% of human error data breaches and it can happen to anyone, including the US Embassy in Australia who accidentally sent out a meeting invitation with a picture of a cat dressed as Cookie Monster in what they described in their apology as a training error.
Whilst this example is amusing it could have been very different.
For sensitive emails encryption is a good idea and many organisations are now also deploying more advanced security solutions that can prevent specific documents from leaving the corporate network.
It’s all about people
Ultimately people will make mistakes but there is no defence for not mitigating against foreseeable risks (again just imagine explaining not mitigating against a foreseeable risk to your Audit Committee, or worse an investigation).
Proactively training staff through a continual process of workforce development around digital skills is not just a good idea, I would argue it is now essential. Additionally IT teams must have access to the right tools to enable them to proactively manage known and foreseeable threats to digital assets.
Making effective use of cloud technology with leading security credentials will also enhance resilience against cyberintrusion and should definitely be high on the menu.
In the context of data protection, as the saying goes, ‘to err is human. To really foul things up requires a computer’ so when you are dealing with both, effective digital coaching and continual training is essential if you’re to avoid your very own Jeffrey Wong moment.
Jamie E Smith, Executive Chairman, C-Learning


Responses