The Best Cybersecurity Tips For Distance Learning
As students and teachers spend more time online under COVID-19 precautions, they become more susceptible to hacking attempts. Since home networks do not provide the increased firewalls protections institutions do, the results of at-home Internet attacks can be far more catastrophic. When navigating the web to conduct research, complete homework, and participate in online lectures, the best safety net students and teachers have are their passwords. Here’s a bit of background.
The History of Passwords
In 1960, MIT’s Compatible Time-Sharing System, known as CTSS, was the first algorithm prompting the use of passwords. Using separate consoles to access a shared mainfraim, multiple users shared each console, but each had their own set of files. To access their individual files, gaining permission to their personal point of entry, each user necessitated the use of passwords.
Just two years later in 1962, the first instance of password theft was recorded. Here’s how:
Alan Scheer, a Ph.D candidate, tested the CTSS’ strength. He was given just 4 hours per week to work on the system; and by printing the system’s password file, he was able to log-in as other users. Simple as that.
The history of passwords is noteworthy to emphasize password and data theft is not new and is only advancing. In fact, passwords are weaker than authentication questions but require far less memory to store in a system. Although this was only a compromise for computers in their infancy, to a degree, this still stands today.
The Rise of Password Hacking
Today, it’s much harder for hackers to gain access to a user’s passwords than the methods of Alan Scheer. However, not much later in history did things begin to change.
In 1988, The Morris Worm became the first computer worm on the Internet. This infected 1 in 10 networked computers within just 24-hours of its development. In similar fashion to Alan Scheer, the intention of The Morris Worm was harmless, but the incident sparked a new era of cybersecurity and gave hackers several new ideas for approaches to theft.
How Your Password Can Help You Stay Protected
As you know, our computers aren’t as advanced as our cellphones. Most of our mobile devices are powered with biometric log-in features; however, the average computer does not do the same. Saying this, your keyboard is your most valuable asset in preventing your personal data from being stolen online.
Being that distance learning is completing on your personal device and personal network, hackers can gain far more information than they could if you were attacked on a computer provided by your institution. For example, a hacker can now obtain your credit card information, address, social security numbers, contact lists, browser history, and more – all while you’re engaged in distance learning.
It’s time to put some armor around your passwords. An analysis of The Morris Worm’s leaked data showed nearly 50% of users had easily guessable passwords. In fact, the most common password was “123456.” Simply putting time into what you’re storing as a password is crucial in lessening your chances of attack.
Think uniquely, something that no one knows but you. Avoid using your birthday, social security number, credit card PIN, home address, name, or any other “general” knowledge about yourself as a password. When setting a password hint, don’t make it hard enough for you to forget.
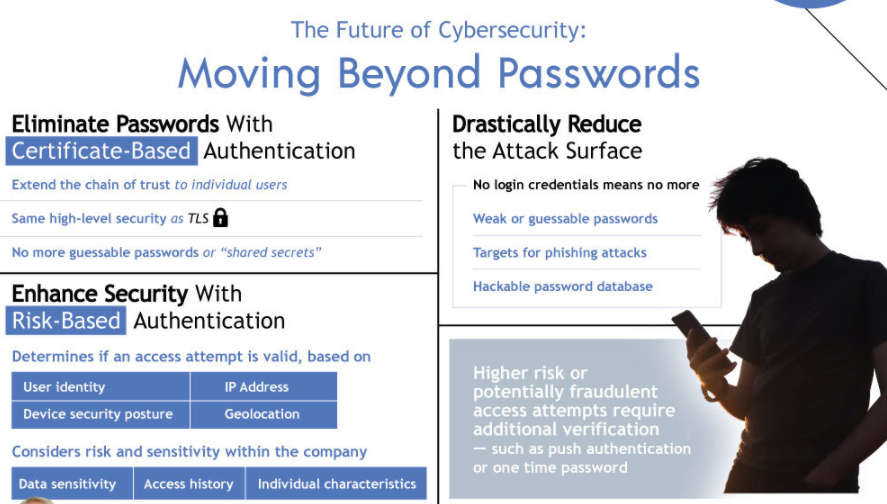
The Future of Cybersecurity: Moving Beyond Passwords
If you have the opportunity to double-shield your accounts and computer with something greater than a traditional password, please do so. Higher risk or potentially fraudulent access attempts require additional verification – such as push authentification or one-time passwords. By double-shielding, you may be able to catch when these kinds of attempts take place.
In the future, we will see passwords being eliminated altogether, and swapped out for certificate-based authentification – as well as enhancing our security with risk-based authentification. In the meantime, it’s important to work smarter, not harder.
How are you staying safe online in your distance learning efforts?










Responses